Implement platform protection
Simulado Summary
0 of 30 Questões completed
Perguntas:
Information
Você já concluiu o simulado antes. Portanto, você não pode reiniciá-lo.
Simulado is loading…
You must sign in or sign up to start the simulado.
Você precisa primeiro terminar os seguintes:
Resultados
Resultados
0 of 30 Questões answered correctly
Seu tempo:
Time has elapsed
You have reached 0 of 0 point(s), (0)
Earned Point(s): 0 of 0, (0)
0 Essay(s) Pending (Possible Point(s): 0)
Categories
- AZ-500 Implement platform protection 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- Current
- Review
- Answered
- Correto
- Incorreto
-
Questão 1 of 30
1. Question
From Azure Security Center, you create a custom alert rule.
You need to configure which users will receive an email message when the alert is triggered.
What should you do?
CorretoIncorreto -
Questão 2 of 30
2. Question
You are configuring and securing a network environment.
You deploy an Azure virtual machine named VM1 that is configured to analyze network traffic.
You need to ensure that all network traffic is routed through VM1.
What should you configure?
CorretoIncorreto -
Questão 3 of 30
3. Question
You have an Azure subscription that contains the virtual networks shown in the following table.
Name Region Subnet VNET1 West US Subnet11 and Subnet12 VNET2 West US 2 Subnet21 VNET3 East US Subnet31 The subscription contains the virtual machines shown in the following table.
Name Network interface Connected to VM1 NIC1 Subnet11 VM2 NIC2 Subnet11 VM3 NIC3 Subnet12 VM4 NIC4 Subnet21 VM5 NIC5 Subnet31 On NIC1, you configure an application security group named ASG1.
On which other network interfaces can you configure ASG1?
CorretoIncorreto -
Questão 4 of 30
4. Question
You have 15 Azure virtual machines in a resource group named RG1.
All the virtual machines run identical applications.
You need to prevent unauthorized applications and malware from running on the virtual machines.
What should you do?
CorretoIncorreto -
Questão 5 of 30
5. Question
You plan to deploy Azure container instances.
You have a containerized application that validates credit cards. The application is comprised of two containers: an application container and a validation container.
The application container is monitored by the validation container. The validation container performs security checks by making requests to the application container and waiting for responses after every transaction.
You need to ensure that the application container and the validation container are scheduled to be deployed together. The containers must communicate to each other only on ports that are not externally exposed.
What should you include in the deployment?
CorretoIncorreto -
Questão 6 of 30
6. Question
You are securing access to the resources in an Azure subscription.
A new company policy states that all the Azure virtual machines in the subscription must use managed disks.
You need to prevent users from creating virtual machines that use unmanaged disks.
What should you use?
CorretoIncorreto -
Questão 7 of 30
7. Question
You have an Azure Kubernetes Service (AKS) cluster that will connect to an Azure Container Registry.
You need to use automatically generated service principal for the AKS cluster to authenticate to the Azure Container Registry.
What should you create?
CorretoIncorreto -
Questão 8 of 30
8. Question
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You use Azure Security Center for the centralized policy management of three Azure subscriptions.
You use several policy definitions to manage the security of the subscriptions.
You need to deploy the policy definitions as a group to all three subscriptions.
Solution: You create an initiative and an assignment that is scoped to a management group.
Does this meet the goal?
CorretoIncorreto -
Questão 9 of 30
9. Question
You have the Azure virtual machines shown in the following table.
Name Operating system State VM1 Windows Server 2012 Running VM2 Windows Server 2012 R2 Running VM3 Windows Server 2016 Stopped VM4 Ubuntu Server 18.04 LTS Running For which virtual machine can you enable Update Management?
CorretoIncorreto -
Questão 10 of 30
10. Question
You have an Azure subscription that contains a user named User1 and an Azure Container Registry named ConReg1.
You enable content trust for ContReg1.
You need to ensure that User1 can create trusted images in ContReg1. The solution must use the principle of least privilege.
Which two roles should you assign to User1? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
CorretoIncorreto -
Questão 11 of 30
11. Question
You have an Azure Container Registry named ContReg1 that contains a container image named image1.
You enable content trust for ContReg1.
After content trust is enabled, you push two images to ContReg1 as shown in the following table.
Name Details image2 Image was pushed with client content trust enabled. image3 Image was pushed with client content trust disable. Which images are trusted images?
CorretoIncorreto -
Questão 12 of 30
12. Question
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You use Azure Security Center for the centralized policy management of three Azure subscriptions.
You use several policy definitions to manage the security of the subscriptions.
You need to deploy the policy definitions as a group to all three subscriptions.
Solution: You create a policy initiative and assignments that are scoped to resource groups.
Does this meet the goal?
CorretoIncorreto -
Questão 13 of 30
13. Question
You have Azure Resource Manager templates that you use to deploy Azure virtual machines.
You need to disable unused Windows features automatically as instances of the virtual machines are provisioned.
What should you use?
CorretoIncorreto -
Questão 14 of 30
14. Question
You have an Azure subscription named Sub1. Sub1 contains a virtual network named VNet1 that contains one subnet named Subnet1.
Subnet1 contains an Azure virtual machine named VM1 that runs Ubuntu Server 18.04.
You create a service endpoint for MicrosoftStorage in Subnet1.
You need to ensure that when you deploy Docker containers to VM1, the containers can access Azure Storage resources by using the service endpoint.
What should you do on VM1 before you deploy the container?
CorretoIncorreto -
Questão 15 of 30
15. Question
You have Azure Resource Manager templates that you use to deploy Azure virtual machines.
You need to disable unused Windows features automatically as instances of the virtual machines are provisioned.
What should you use?
CorretoIncorreto -
Questão 16 of 30
16. Question
You are configuring an Azure Kubernetes Service (AKS) cluster that will connect to an Azure Container Registry.
You need to use the auto-generated service principal to authenticate to the Azure Container Registry.
What should you create?
CorretoIncorreto -
Questão 17 of 30
17. Question
You have an Azure subscription that contains the Azure virtual machines shown in the following table.
Name Operating system VM1 Windows 10 VM2 Windows Server 2016 VM3 Windows Server 2019 VM4 Ubuntu Server 18.04 LTS You create an MDM Security Baseline profile named Profile1.
You need to identify to which virtual machines Profile1 can be applied.
Which virtual machines should you identify?
CorretoIncorreto -
Questão 18 of 30
18. Question
You have Azure Resource Manager templates that you use to deploy Azure virtual machines.
You need to disable unused Windows features automatically as instances of the virtual machines are provisioned.
What should you use?
CorretoIncorreto -
Questão 19 of 30
19. Question
You have an Azure virtual machine named VM1.
From Azure Security Center, you get the following high-severity recommendation: “Install endpoint protection solutions on virtual machine”.
You need to resolve the issue causing the high-severity recommendation.
What should you do?
CorretoIncorreto -
Questão 20 of 30
20. Question
You have an Azure subscription that contains a virtual network. The virtual network contains the subnets shown in the following table.
Name Has a network Security group (NSG) associated to the virtual subnet Subnet1 Yes Subnet2 No The subscription contains the virtual machines shown in the following table
Name Has a network Security group (NSG) associated to the virtual machine Connected to VM1 No Subnet1 VM2 No Subnet2 VM3 No Subnet1 VM4 Yes Subnet2 You enable just in time (JIT) VM access for all the virtual machines.
You need to identify which virtual machines are protected by JIT.
Which virtual machines should you identify?
CorretoIncorreto -
Questão 21 of 30
21. Question
You have Azure Resource Manager templates that you use to deploy Azure virtual machines.
You need to disable unused Windows features automatically as instances of the virtual machines are provisioned.
What should you use?
CorretoIncorreto -
Questão 22 of 30
22. Question
From Azure Security Center, you enable Azure Container Registry vulnerability scanning of the images in Registry1.
You perform the following actions:
- Push a Windows image named Image1 to Registry1.
- Push a Linux image named Image2 to Registry1.
- Push a Windows image named Image3 to Registry1.
- Modify Image1 and push the new image as Image4 to Registry1.
- Modify Image2 and push the new image as Image5 to Registry1.
Which two images will be scanned for vulnerabilities? Each correct answer presents a complete solution.
NOTE: Each correct selection is worth one point.
CorretoIncorreto -
Questão 23 of 30
23. Question
You have the Azure virtual machines shown in the following table.
Name Operating system Region Resource group VM1 Windows Server 2012 East US RG1 VM2 Windows Server 2012 R2 West Europe RG1 VM3 Windows Server 2016 West Europe RG2 VM4 Red Hat Enterprise Linux 7.4 East US RG2 You create an Azure Log Analytics workspace named Analytics1 in RG1 in the East US region.
Which virtual machines can be enrolled in Analytics1?
CorretoIncorreto -
Questão 24 of 30
24. Question
You are testing an Azure Kubernetes Service (AKS) cluster. The cluster is configured as shown below:
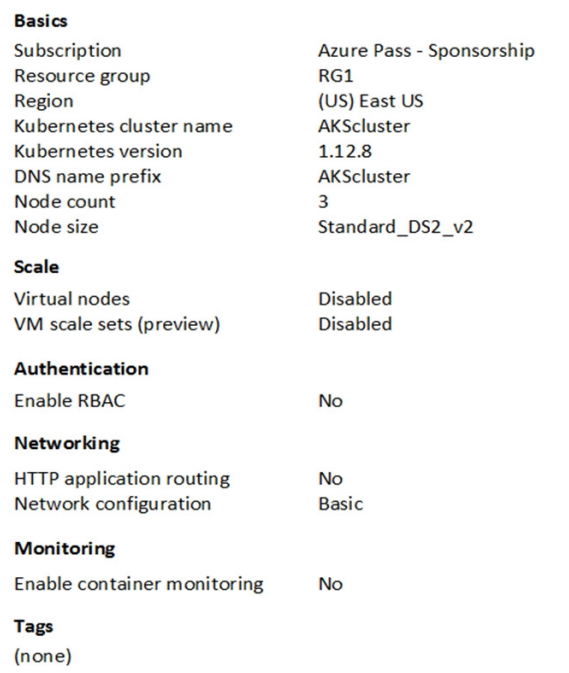
You plan to deploy the cluster to production. You disable HTTP application routing.
You need to implement application routing that will provide reverse proxy and TLS termination for AKS services by using a single IP address.
What should you do?
CorretoIncorreto -
Questão 25 of 30
25. Question
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You use Azure Security Center for the centralized policy management of three Azure subscriptions.
You use several policy definitions to manage the security of the subscriptions.
You need to deploy the policy definitions as a group to all three subscriptions.
Solution: You create a policy definition and assignments that are scoped to resource groups.
Does this meet the goal?
CorretoIncorreto -
Questão 26 of 30
26. Question
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You use Azure Security Center for the centralized policy management of three Azure subscriptions.
You use several policy definitions to manage the security of the subscriptions.
You need to deploy the policy definitions as a group to all three subscriptions.
Solution: You create a resource graph and an assignment that is scoped to a management group.
Does this meet the goal?
CorretoIncorreto -
Questão 27 of 30
27. Question
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have an Azure subscription. The subscription contains 50 virtual machines that run Windows Server 2012 R2 or Windows Server 2016.
You need to deploy Microsoft Antimalware to the virtual machines.
Solution: You add an extension to each virtual machine.
Does this meet the goal?
CorretoIncorreto -
Questão 28 of 30
28. Question
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have an Azure subscription. The subscription contains 50 virtual machines that run Windows Server 2012
R2 or Windows Server 2016.
You need to deploy Microsoft Antimalware to the virtual machines.
Solution: You connect to each virtual machine and add a Windows feature.
Does this meet the goal?
CorretoIncorreto -
Questão 29 of 30
29. Question
You have an Azure Active Directory (Azure AD) tenant named Contoso.com and an Azure Kubernetes Service (AKS) cluster AKS1.
You discover that AKS1 cannot be accessed by using accounts from Contoso.com.
You need to ensure AKS1 can be accessed by using accounts from Contoso.com. The solution must minimize administrative effort.
What should you do first?
CorretoIncorreto -
Questão 30 of 30
30. Question
You have an Azure subscription that contains an Azure Container Registry named Registry1. The subscription uses the Standard use tier of Azure Security Center.
You upload several container images to Register1.
You discover that vulnerability security scans were not performed.
You need to ensure that the images are scanned for vulnerabilities when they are uploaded to Registry1.
What should you do?
CorretoIncorreto
